01
Oct 2019


 3. Roles Assignments Defined
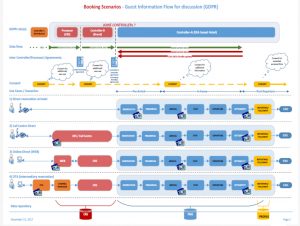
3. Roles Assignments Defined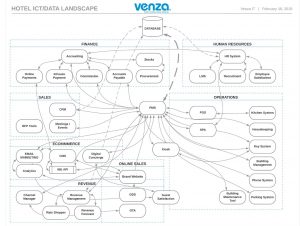 4. Legacy Data Risk Assessed and Cessation of Unlawful Processes Documented
4. Legacy Data Risk Assessed and Cessation of Unlawful Processes Documented 5. Policies Assessed and Published
5. Policies Assessed and Published 6. Security Allocated to the Professionals
6. Security Allocated to the Professionals 7. SARs, Breach and Purge Procedures Formulated
7. SARs, Breach and Purge Procedures Formulated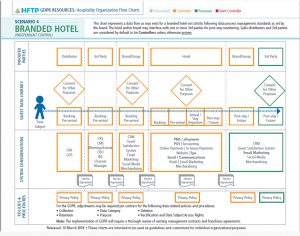 8. Agreements (DPA, etc.) Assessed
8. Agreements (DPA, etc.) Assessed
 10. Training & Awareness Program Conducted and Documented
10. Training & Awareness Program Conducted and Documented