MOVEit Breach Underscores Threats to Hotels from Vendor Vulnerabilities
Another week, another breach.
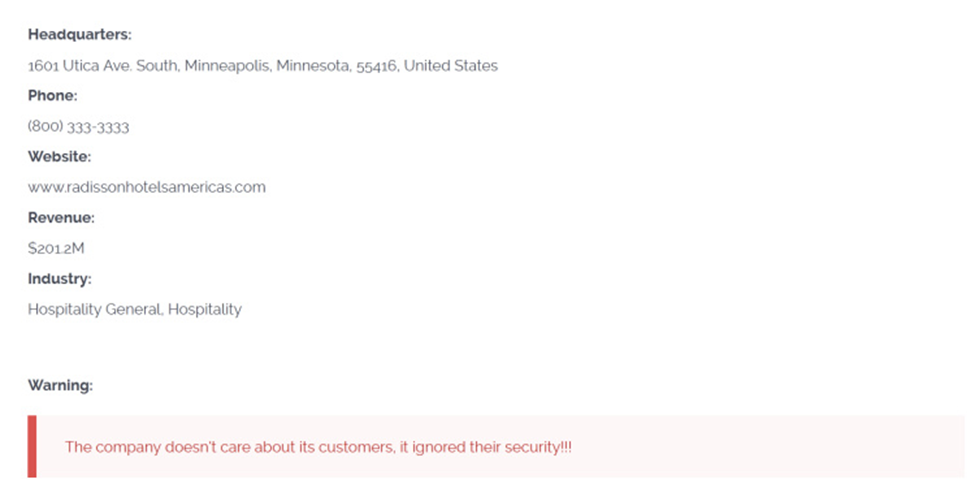
This week, Choice Hotels, the parent company of Radisson Hotels America, announced that guest data from the franchisor had been compromised in the recent MOVEit breach.
While the number of victims has not yet been disclosed, Radisson Hotels America operates over 600 hotels, raising the prospect of a large and potentially extremely costly impact.
The case provides yet another example of the risks posed by third-party vendors and the importance of security not only for your own organization, but also the supply chain it relies on.
What Happened
MOVEit is a third-party managed file transfer software product, used by major companies in the energy, financial, retail, and legal sectors, as well as hospitality.
In late May 2023, MOVEit was targeted by CL0P, a Russian ransomware group. Using a common hacking technique known as SQL injection, the group was able to exploit a zero-day vulnerability in the software to expose the personal data of over 15 million people from at least 122 organizations.
Among the companies affected was Radisson Hotels America. CL0P gained access to sensitive information included in Radisson’s guest records. Although the group has not yet posted the information online, it has threatened to do so. Radisson Hotels America is moving forward with preemptively notifying potentially affected guests.
What We Can Learn
Like the 2018 Marriott breach, the incident at Radisson was caused by products supplied by third-party vendors. This serves as a reminder that organizations are only as secure as the products and companies that they rely on.
To protect your organization from the financial and reputational consequences of such a breach, VENZA recommends the following steps:
1. Use Vendor Management software to certify upstream compliance and manage risk. Recording and tracking the security status of vendors can be complex and time consuming, but new software solutions can greatly simplify and streamline the process. VENZA offers access to state-of-the-art solutions that allow you to ensure that your vendors are adhering to best practices and minimizing their—and your—risk.
2. Conduct an immediate inventory. To ensure that you have not been exposed to the MOVEit breach, review your assets and data and verify that there is no expose. While doing so, catalog your authorized devices and make sure that there are no unauthorized devices or software present on your system.
3. Use permissions and network segmentation to limit the scope of third-party software. It may not be possible to fully vet every tool that you use, but you can limit the impact of a breach outside your organization by reducing the range of access that hackers can have through them. Narrowly circumscribe admin access and use the principle of less admin privilege to allow users only the absolute minimum permissions needed to complete their tasks.
4. Stay up to date on the latest best practices with continuing education. To find out more about staying secure while using third-party tools, check out VENZA’s recent edition of the Hospitality Webinar Series on this topic.
Feeling overwhelmed? Don’t be. VENZA is here to help. Cybersecurity is complex, but in partnership with us, your company can get started in as little as one month. Get a live demonstration today by contacting our Customer Success Team. Ready to elevate your game? Contact Sales to discuss signing up for our programs or adding new solutions to your contract.
***
Take VENZA’s free Phishing Test to assess gaps in your human firewall today!

Training your personnel to recognize and report phishing attempts is essential to protecting your guests and their data. Get started by determining your risk and readiness level using this free tool.
***
Want to stay informed? Subscribe to the free VENZA Echo now. You’ll receive a monthly digest with the highlights of our weekly article series and important product updates and news from VENZA.
